Why Legacy Infrastructure Is Your Biggest Cybersecurity Blind Spot
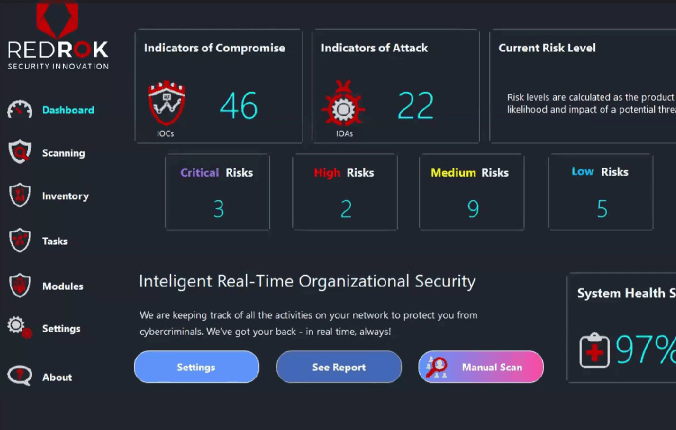
Insights from RedRok’s latest webinar: Master Your Internal Infrastructure with with RedRok's co-founders: Alon Kogan & Nitzan Levi Most organizations are investing heavily in AI, cloud migration, and digital transformation yet a critical security problem persists quietly…